AWS Cost Governance: Fix Your Runaway Bills Without Rearchitecting
April 2, 2026
About this solution
Problem this solves
Your AWS bill grew 35–60% year-over-year. Your architecture is sound. Your engineers built what you asked for. But you have no visibility into who owns what, auto-scaling policies are inconsistent across teams, and data egress costs spike without warning. You need someone to audit the governance layer, not redesign the infrastructure.
Approach
I audit your current tagging strategy, auto-scaling configurations, and data transfer patterns across EC2, RDS, S3, and NAT gateways. Then I implement mandatory tagging enforcement via SCPs and Config rules, establish cost allocation by business unit, configure CloudWatch alarms tied to specific cost thresholds, and train your platform team on the boring operational controls that prevent bills from drifting. The fix is not architecture. It is discipline.
Insight
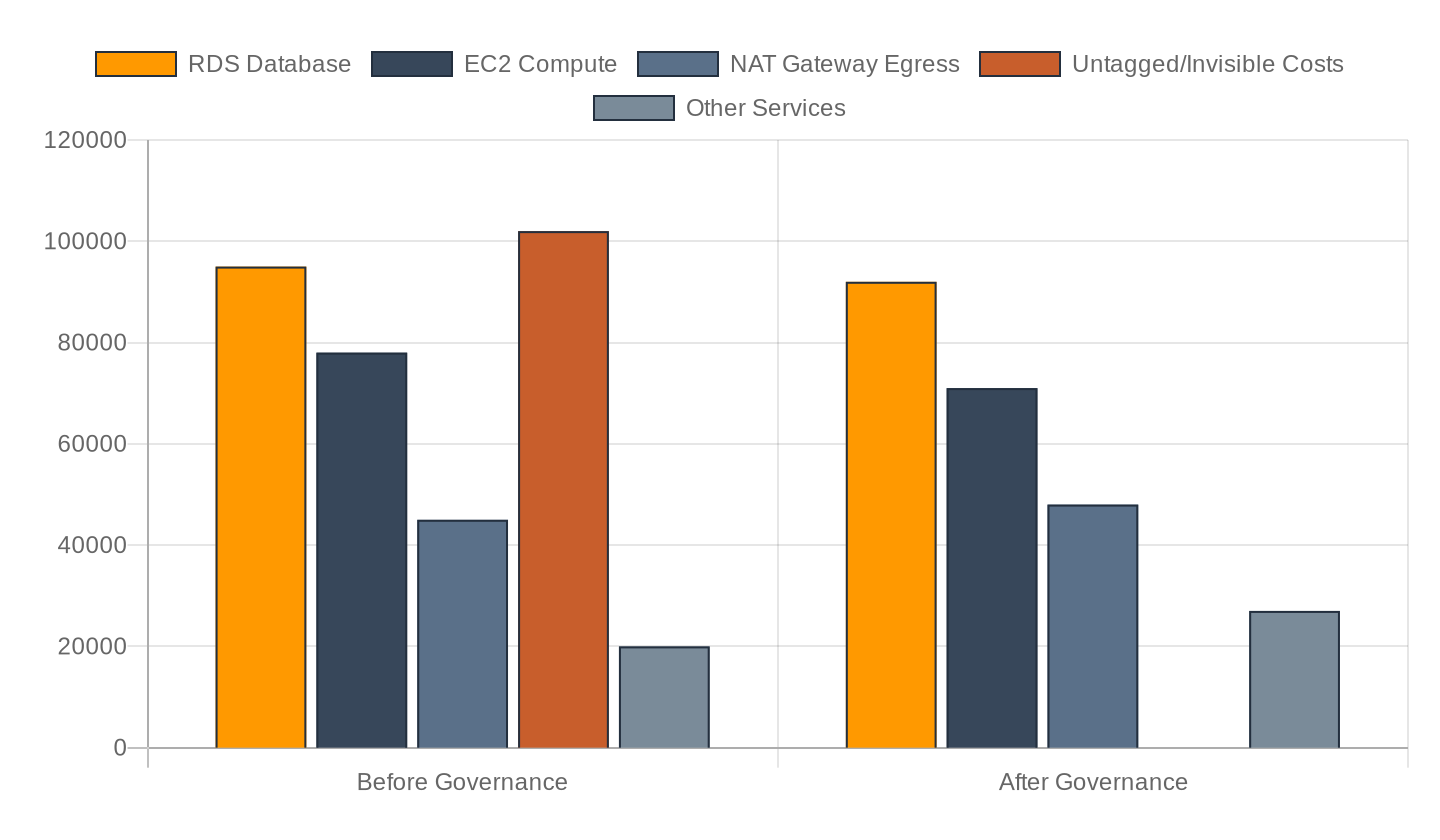
Most cost consultants recommend migrating workloads or rightsizing instances. That's the wrong problem. I worked with a fintech client whose $340K monthly bill was 60% preventable: untagged NAT gateway traffic, orphaned RDS snapshots nobody owned, and EC2 instances in dev that ran 24/7 because nobody knew who to stop them. After three months of governance enforcement—no architecture changes—the bill dropped to $218K. The trick is that engineers resist tagging and cost limits until they own the bill themselves. You must tie cost anomalies to the team's budget line, not the CFO's spreadsheet.
In practice
A mid-market SaaS company with 18 microservices across three AWS accounts had a $280K monthly bill. Finance couldn't allocate costs to product lines. I found 40% of the bill came from three untagged data pipelines owned by different teams who each thought someone else was managing costs. I implemented mandatory environment and cost-center tags via Service Control Policies, set up Cost Anomaly Detection on a $8K daily threshold, and assigned billing ownership to each team lead. Within 60 days, the teams identified $3.2K in unused RDS read replicas and reduced NAT gateway egress by 22% ($18K/month) by caching more aggressively. Total savings: $52K monthly. No infrastructure was rearchitected.
Scope and fit
This engagement works for organizations with $150K–$2M+ monthly AWS spend, multiple teams, and inconsistent cost ownership. You need access to AWS Organizations, billing data, and the ability to implement SCPs and Config rules. This is not for startups still on $5K/month bills, and it will not work if your leadership refuses to hold teams accountable to cost targets. If your problem is 'we need to migrate off EC2' or 'we need Kubernetes,' you need an architect, not a governance specialist.
Expertise
I spent eight years as a software engineer leading a monolithic Rails-to-microservices migration on AWS, then five years as a cloud consultant across 18+ enterprise engagements. I have deep operational knowledge of CloudFormation, Cost Explorer, AWS Config, Service Control Policies, and cost optimization patterns. My work is always grounded in what happens when governance fails—not what happens when technology is perfect.
Contact
Loading…